Aurysia Shield
Endpoint protection, cloud workload security, and regulatory compliance — with real-time threat detection and automated incident response built in.
15M+
Endpoints Protected
3,000+
Detection Rules
12
Security Modules
99.9%
Uptime SLA
YourAttackSurfaceIsGrowing.YourVisibilityIsn't.
Fragmented security tools create blind spots. Your SIEM sees logs but misses endpoints. Your EDR sees endpoints but misses cloud. Alert fatigue buries real threats under thousands of false positives.
Compliance gaps widen with every new regulation. Your security team is stretched thin across tools that don't talk to each other — while adversaries move laterally through the cracks.
FourComponents.OneUnifiedPlatform.
Shield operates as a closed-loop security system — from endpoint data collection through centralized analysis to real-time threat visualization and response.
12SecurityModules.ZeroBlindSpots.
Configuration Assessment
Shield monitors system and application configuration settings to ensure compliance with your security policies, standards, and hardening guides. Agents perform periodic scans to detect misconfigurations or security gaps that can be exploited by threat actors. Customizable checks align with your organization's needs, with alerts including remediation recommendations and regulatory mapping.
Learn More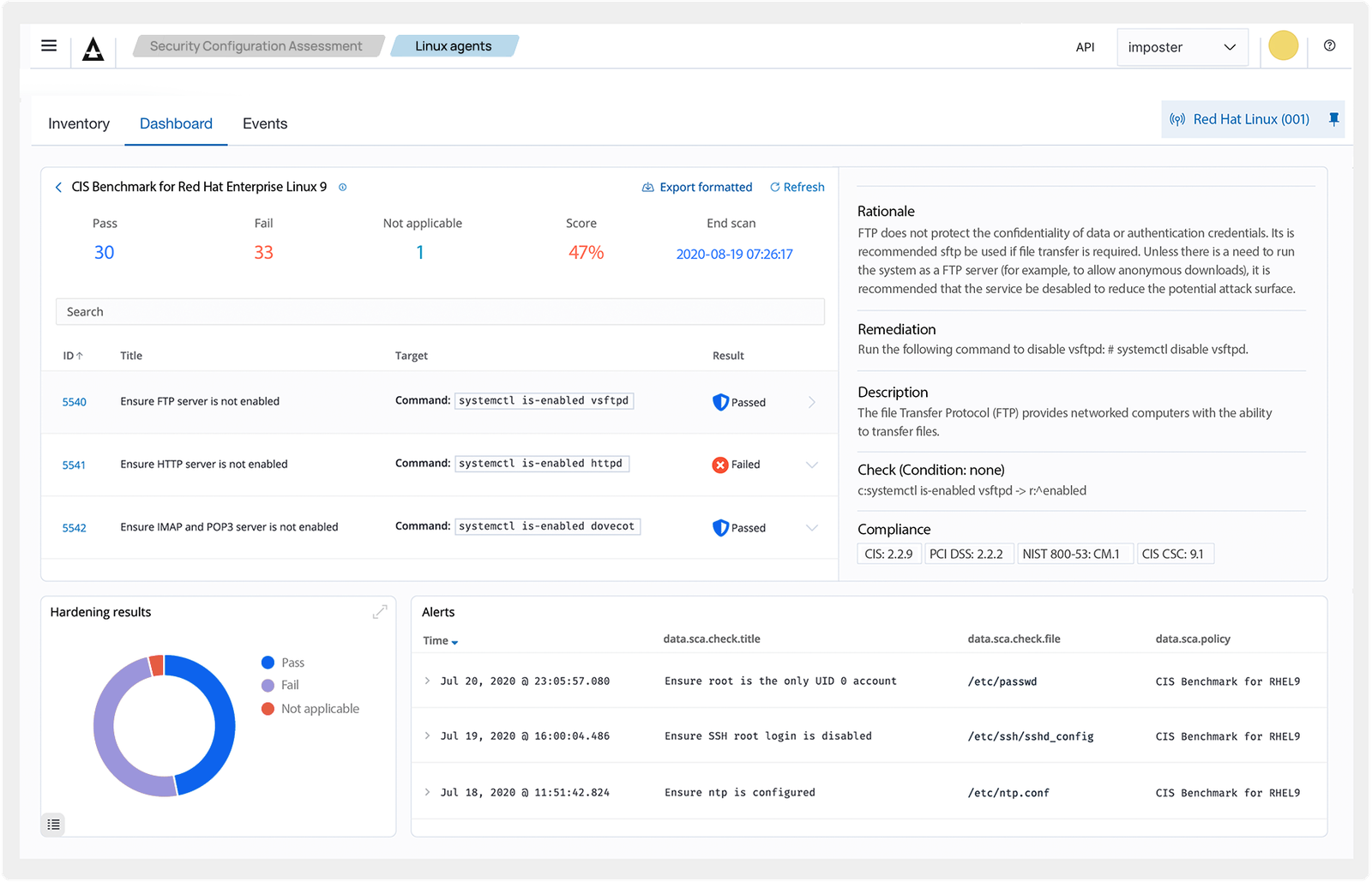
Tap image to zoom
Malware Detection
Detect malicious activities and indicators of compromise on endpoints resulting from malware infection or cyberattack. Shield's out-of-the-box ruleset combined with Security Configuration Assessment, Rootcheck, and File Integrity Monitoring identifies anomalies and malicious behavior — fully configurable to your organization's requirements.
Learn More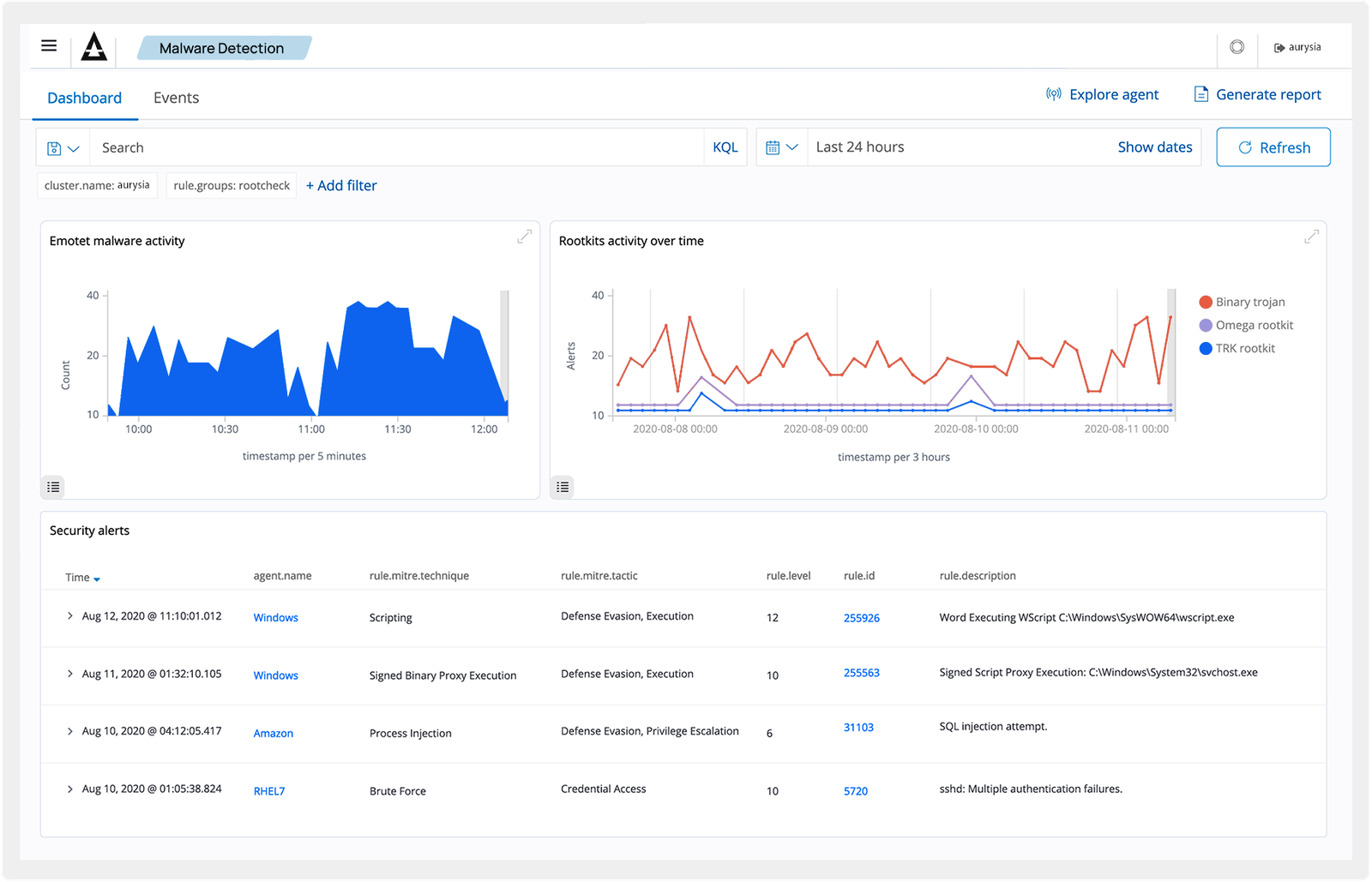
Tap image to zoom
File Integrity Monitoring
Monitor the file system in real time — identifying changes in content, permissions, ownership, and attributes of critical files. Natively identify users and applications used to create or modify files. Combine with threat intelligence to identify compromised endpoints and meet PCI DSS, NIST, and other regulatory compliance standards.
Learn More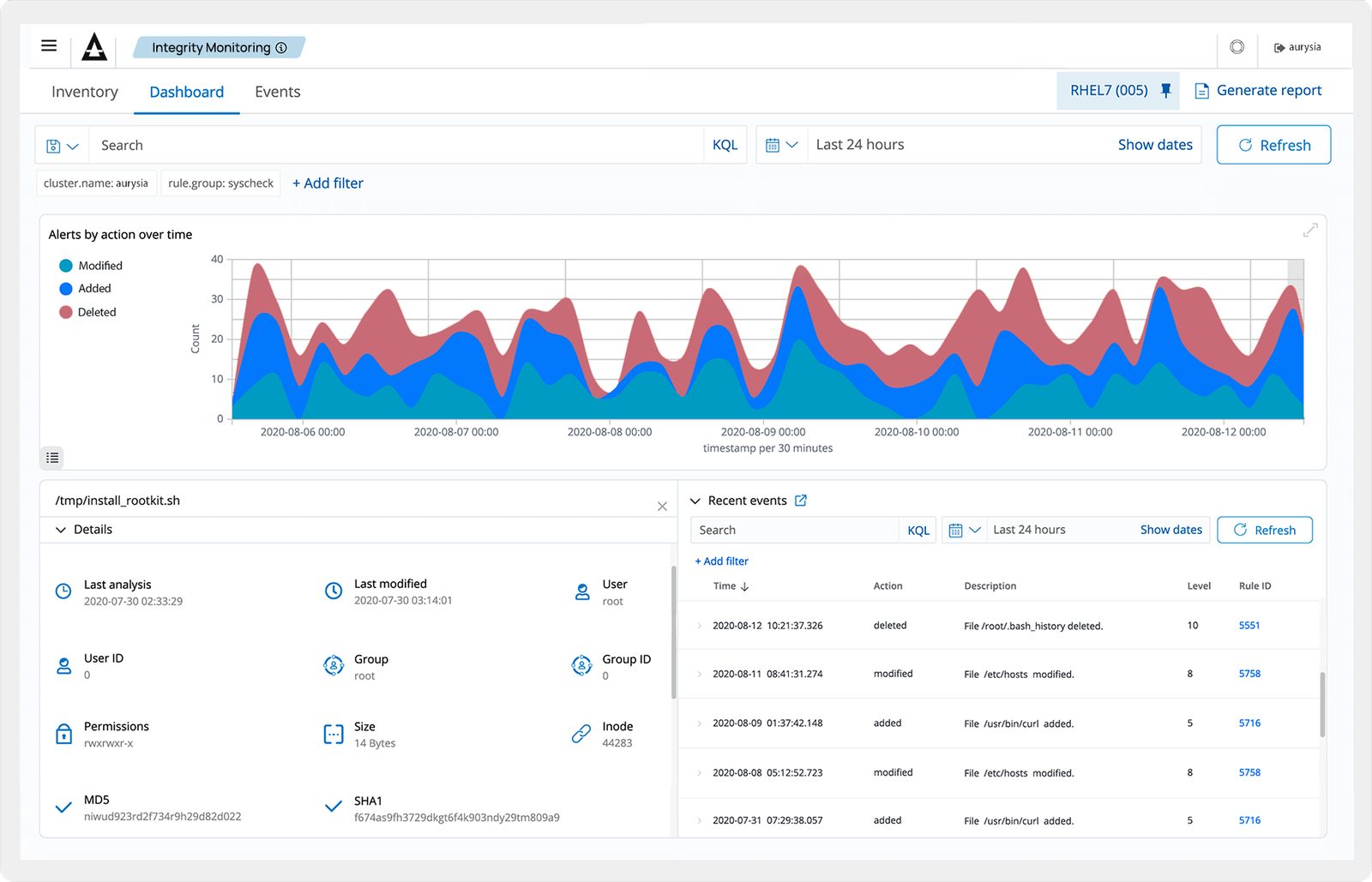
Tap image to zoom
Threat Hunting
Comprehensive visibility into monitored endpoints and infrastructure with log retention, indexing, and querying capabilities. Detection rules mapped against the MITRE ATT&CK framework aid investigation of tactics, techniques, and procedures used by attackers. Integrates with third-party threat intelligence feeds for enhanced hunting.
Learn More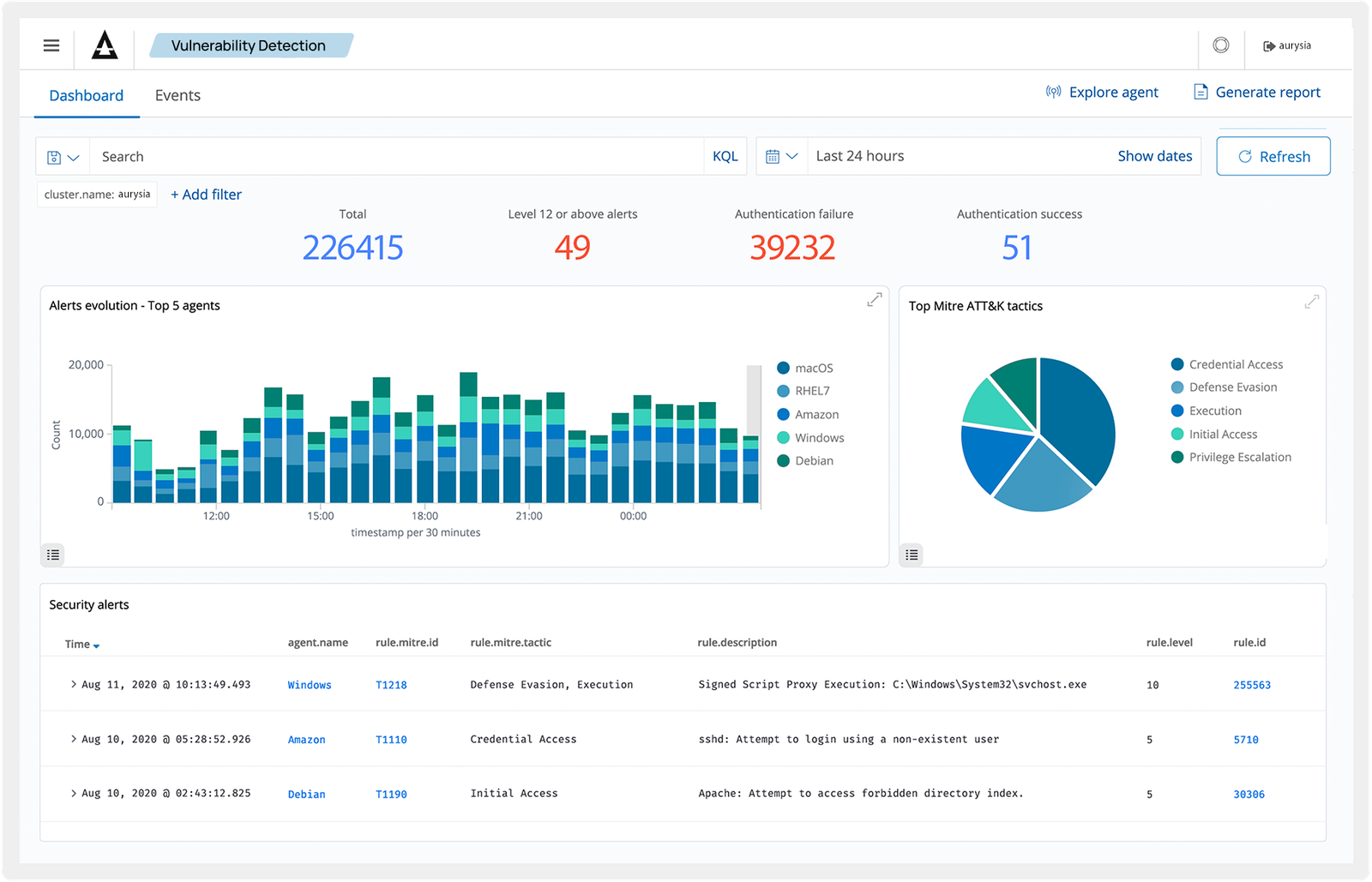
Tap image to zoom
Log Data Analysis
Shield agents collect operating system and application logs, securely forwarding them to the central engine for rule-based analysis and storage. Detection rules identify application errors, misconfigurations, malicious activities, policy violations, and various other security and operational issues.
Learn More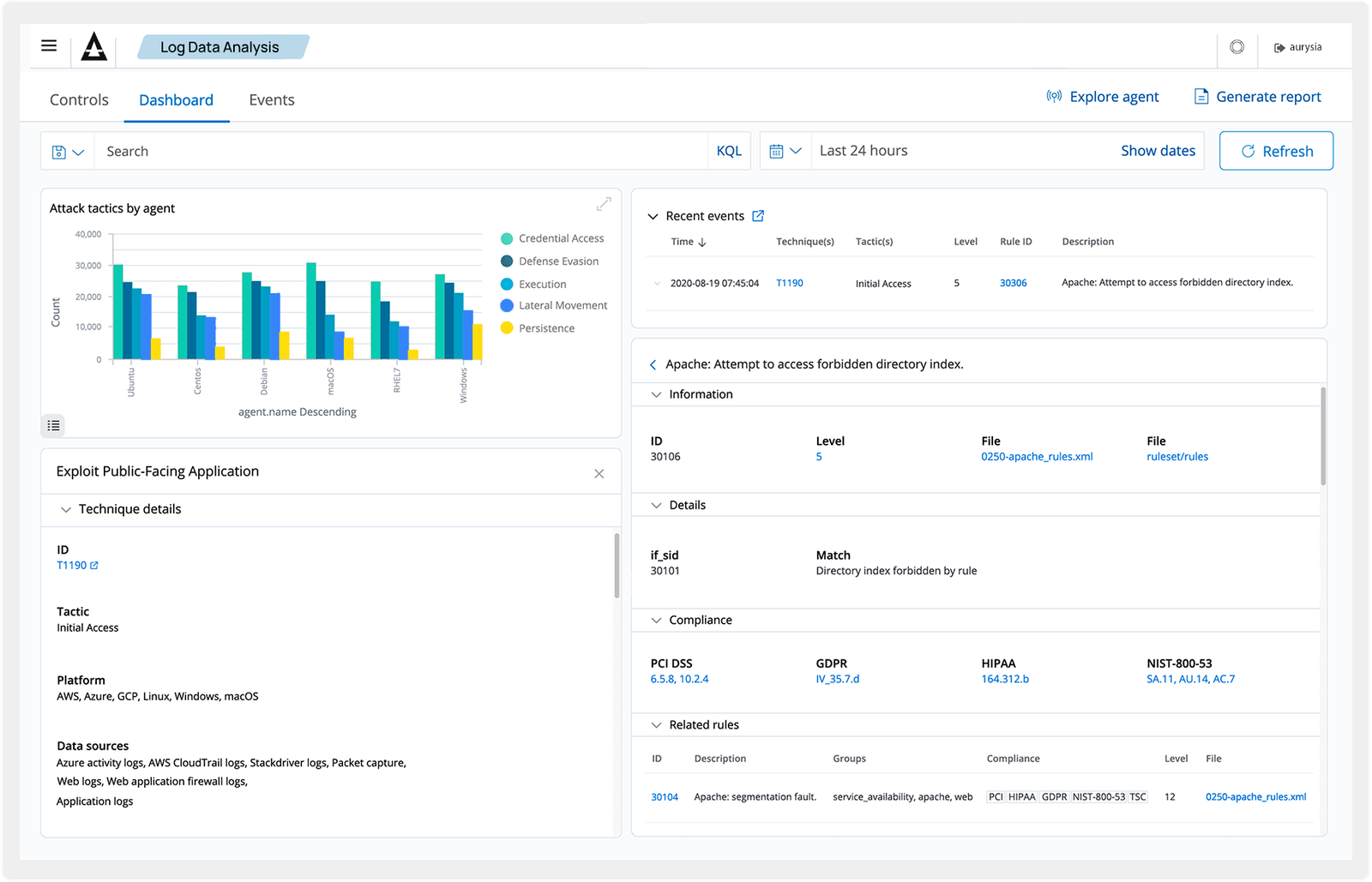
Tap image to zoom
Vulnerability Detection
Agents pull software inventory data and correlate it with continuously updated CVE databases to identify known vulnerable software. Automated vulnerability detection helps you find flaws in critical assets and take corrective action before attackers exploit them.
Learn More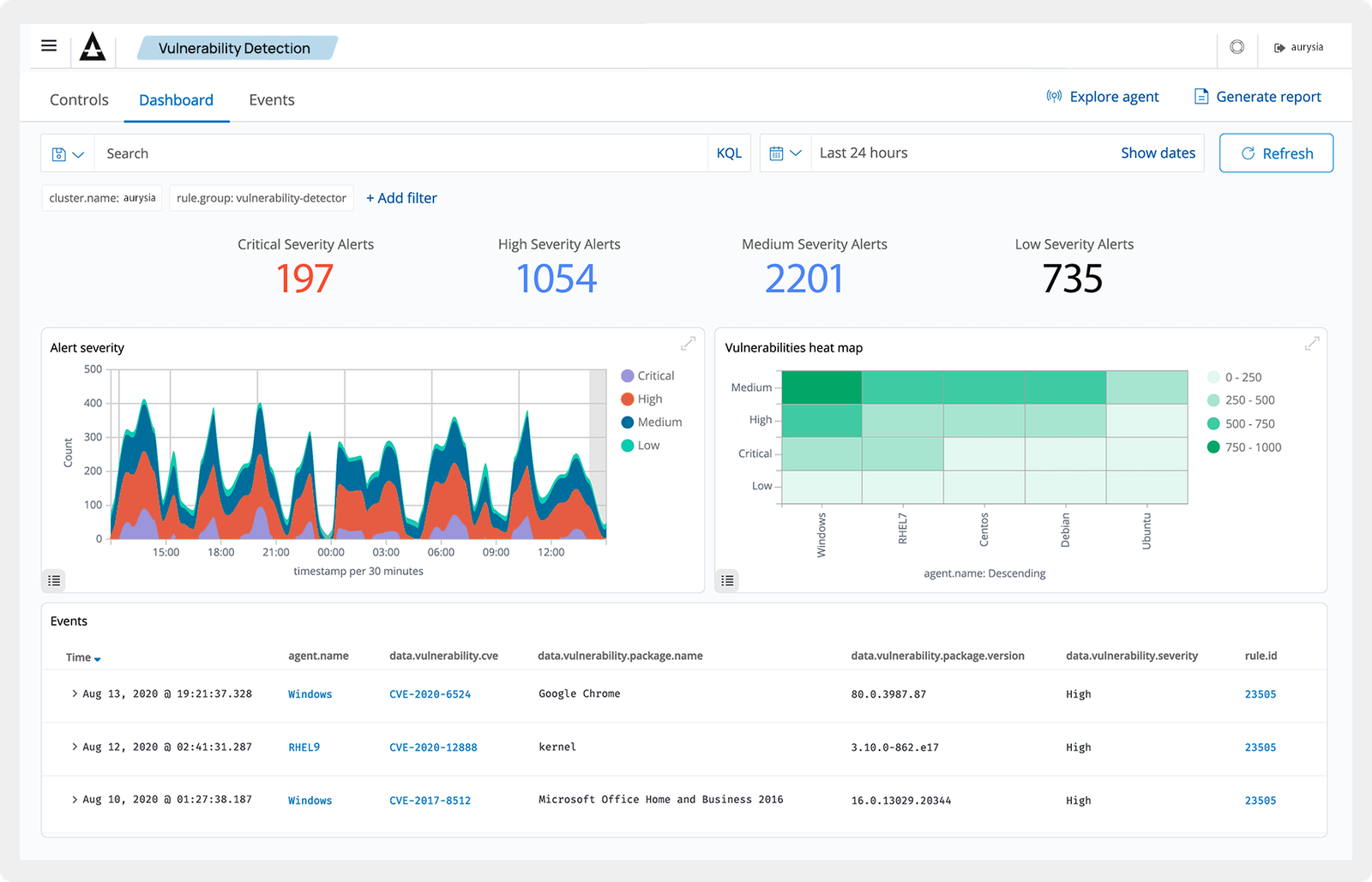
Tap image to zoom
Incident Response
Out-of-the-box active responses perform countermeasures against ongoing threats — blocking network access, isolating endpoints, and executing remote commands. Identify indicators of compromise (IOCs) and perform forensic incident response tasks directly from the Shield Console.
Learn More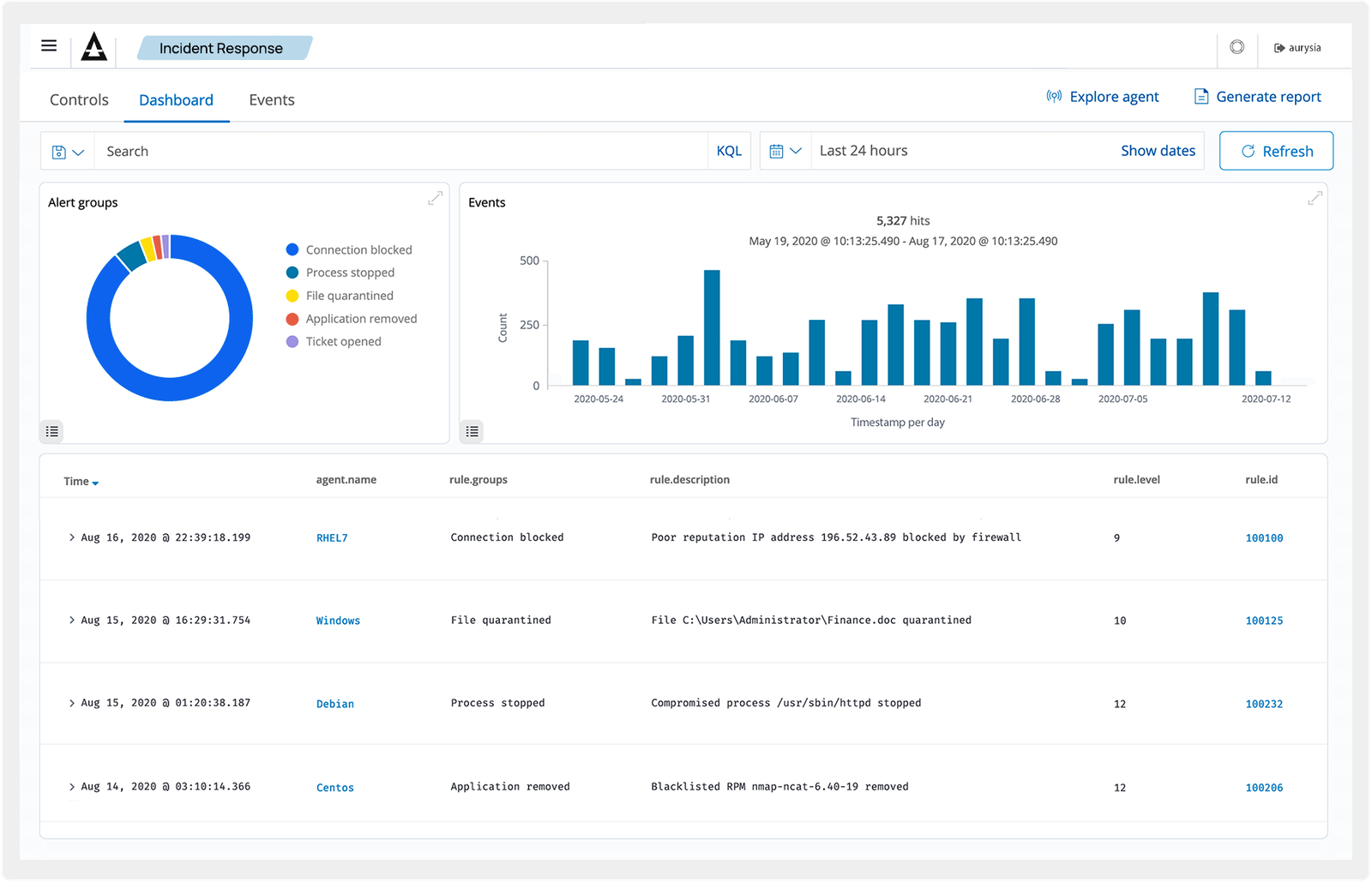
Tap image to zoom
Regulatory Compliance
Shield provides the security controls necessary for industry standards and regulations. File Integrity Monitoring, Security Configuration Assessment, vulnerability detection, and system inventory — combined with scalability and multi-platform support — meet technical compliance requirements for PCI DSS, NIST, TSC, and HIPAA.
Learn More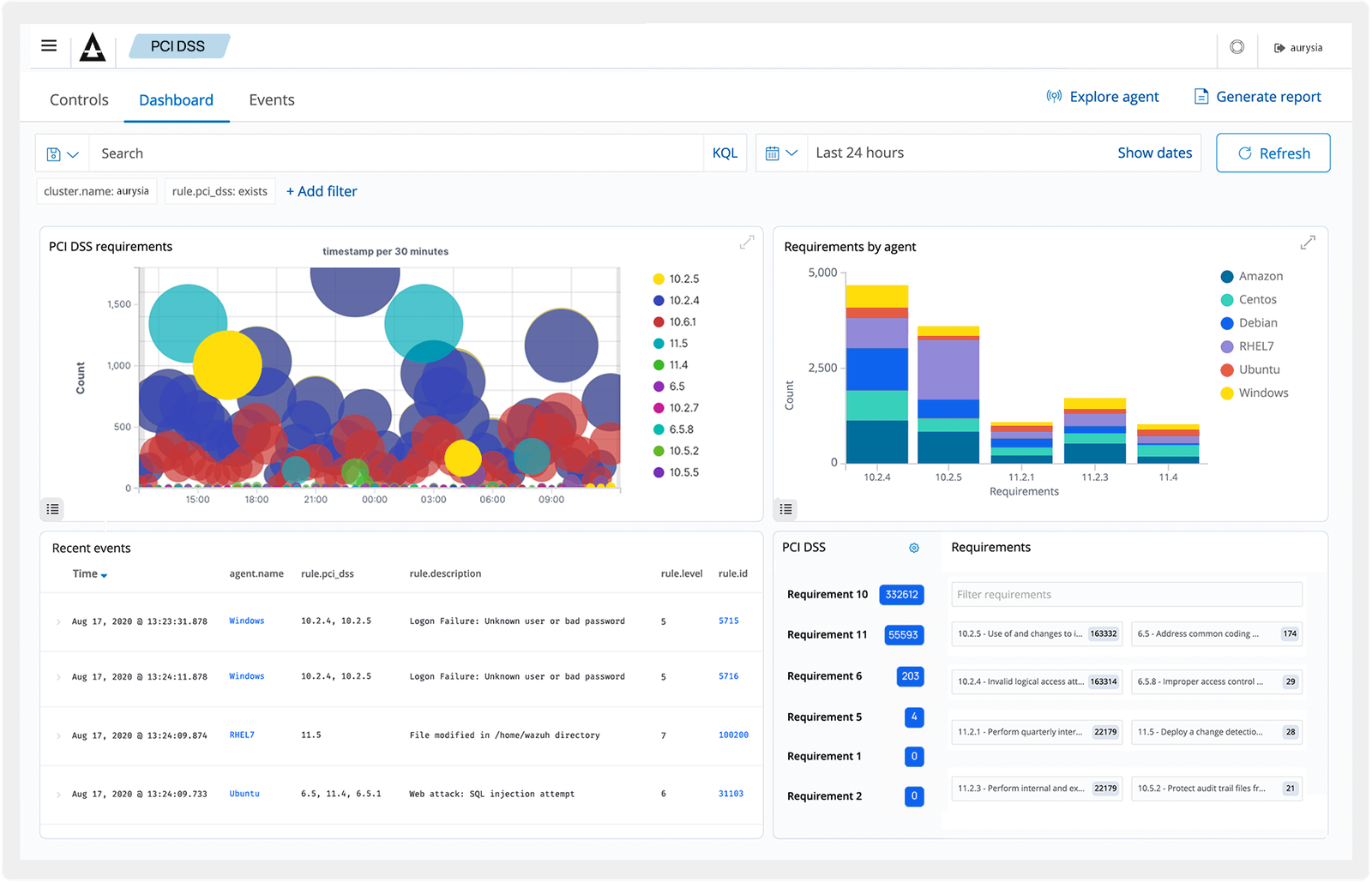
Tap image to zoom
IT Hygiene
Build an up-to-date inventory of all monitored endpoints — installed applications, running processes, open ports, hardware, and OS information. Optimize asset visibility and maintain IT hygiene across your entire infrastructure.
Learn More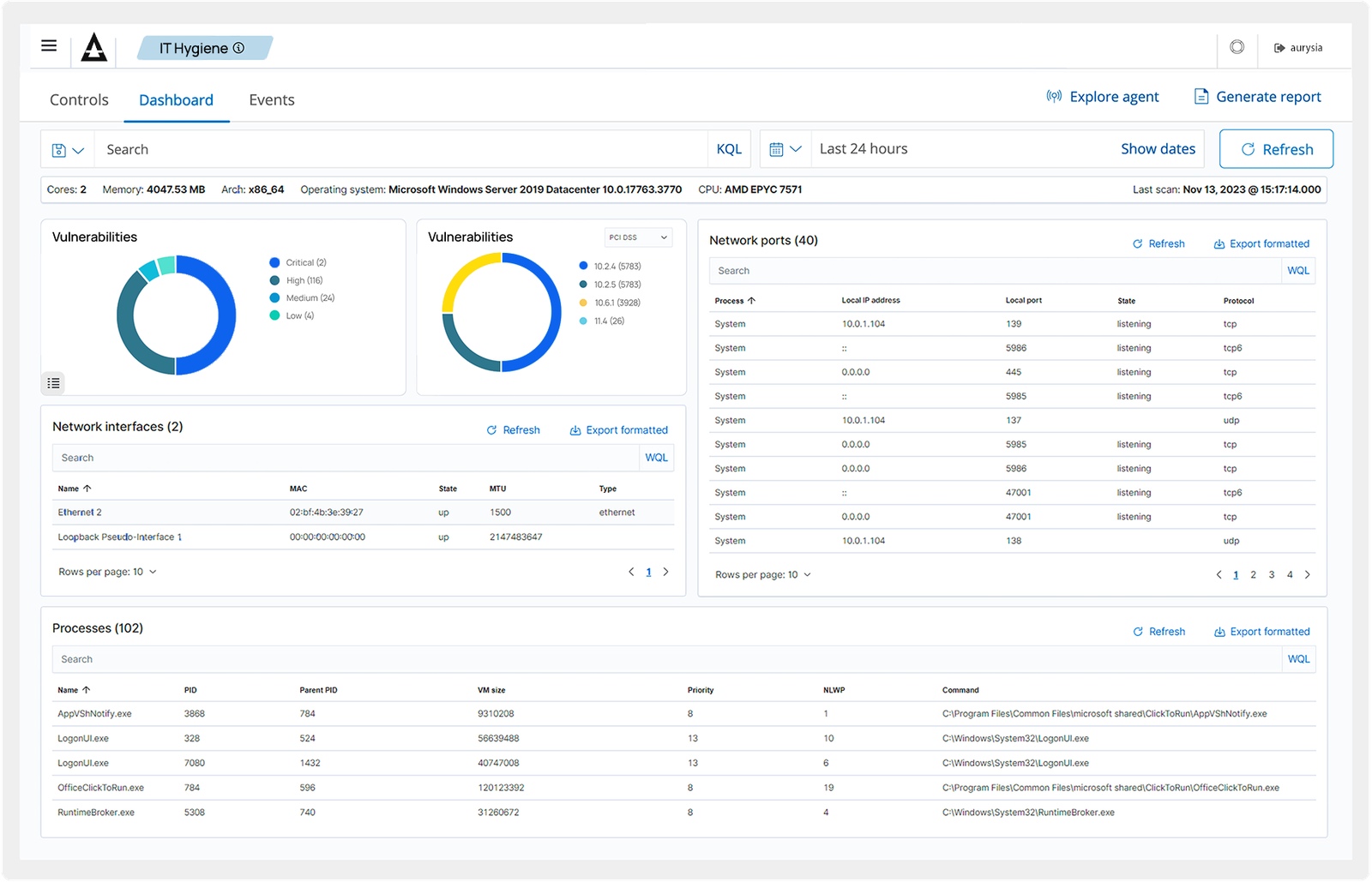
Tap image to zoom
Container Security
Security visibility into Docker hosts and containers — monitoring behavior, detecting threats, vulnerabilities, and anomalies. Native Docker engine integration monitors images, volumes, network settings, and running containers with continuous runtime analysis and alerting.
Learn More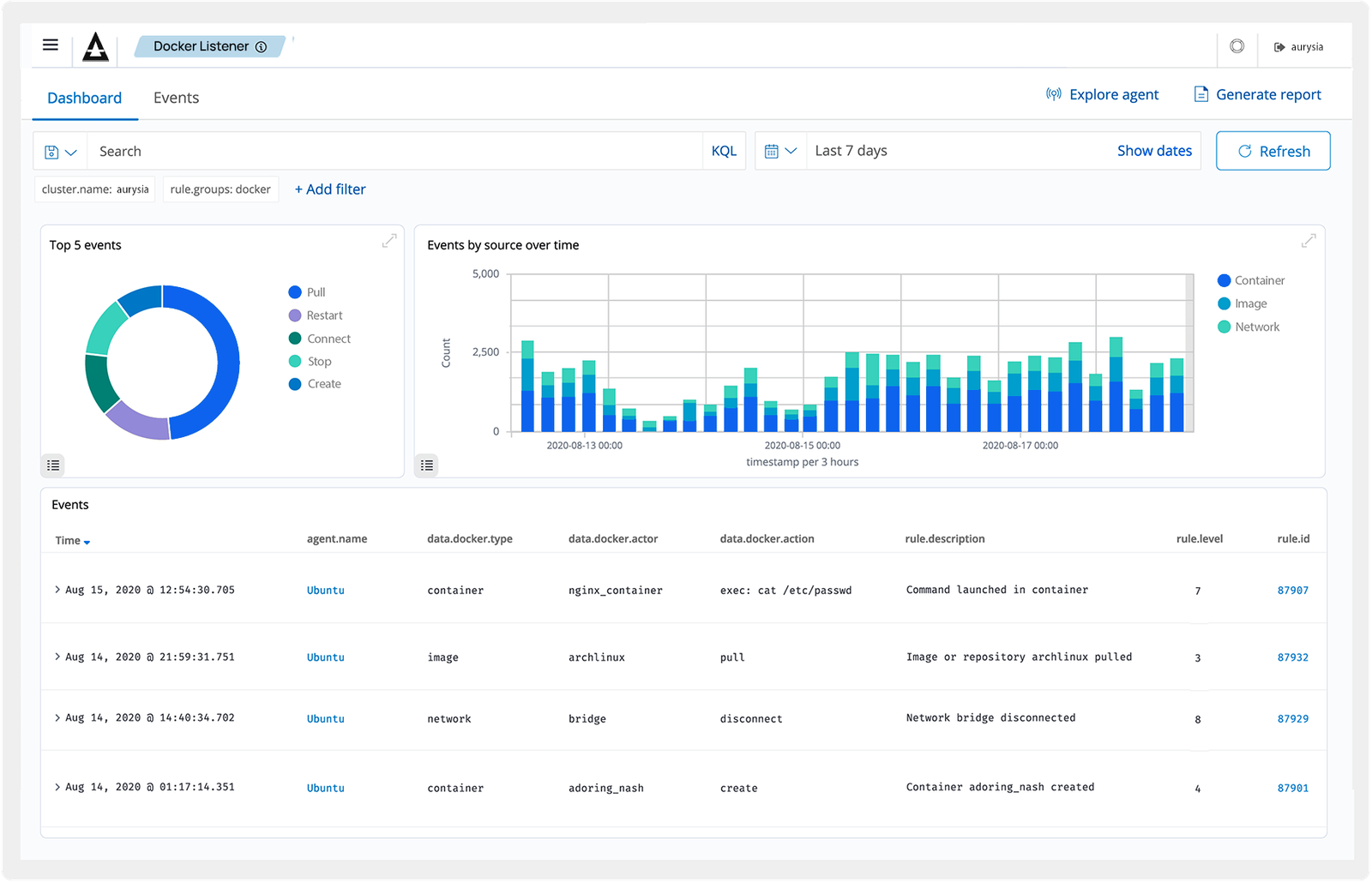
Tap image to zoom
Posture Management
Integrate with cloud platforms to collect and aggregate security data. Shield alerts on discovered security risks and vulnerabilities, ensuring compliance with regulatory standards across your cloud infrastructure.
Learn More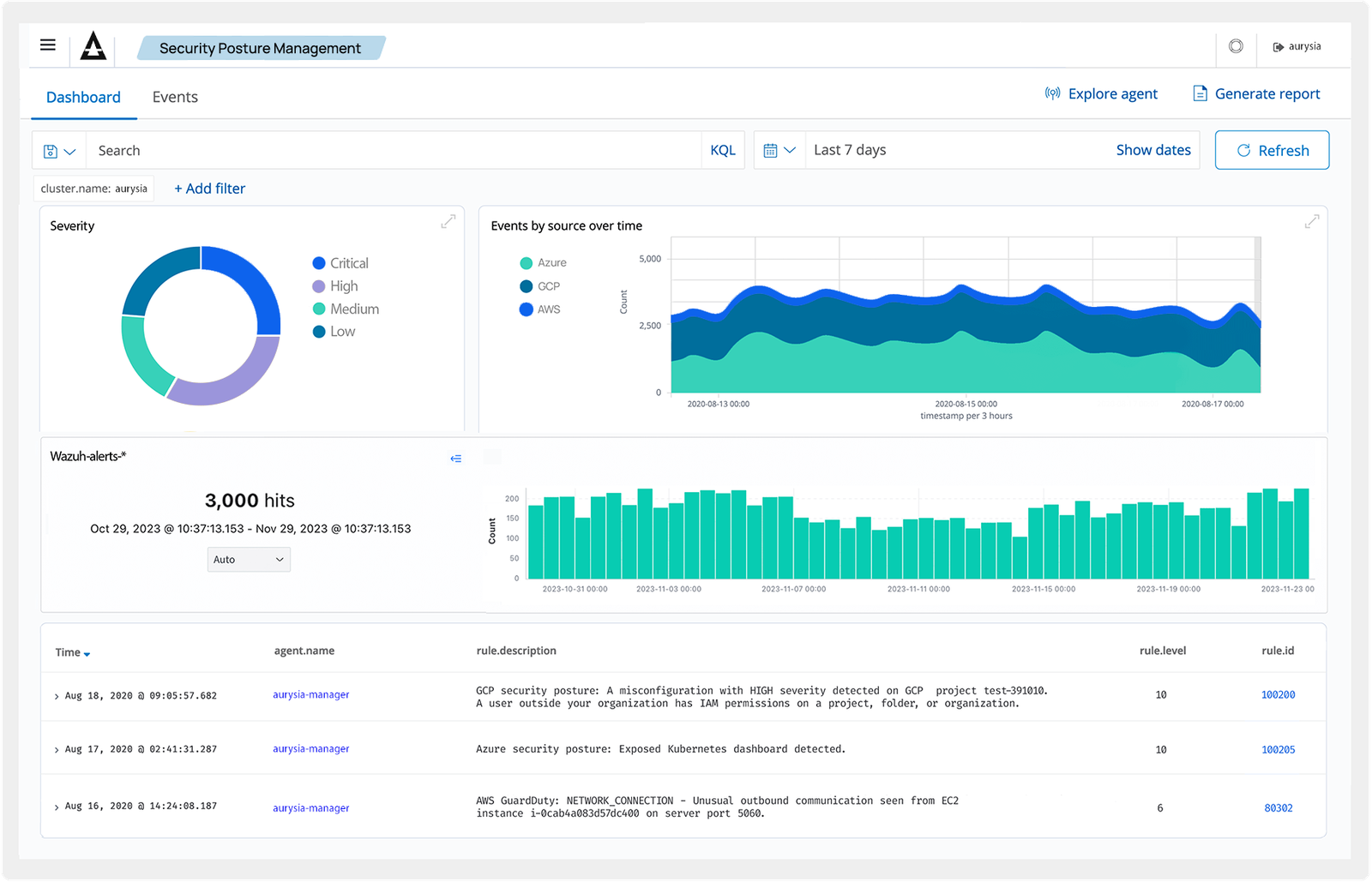
Tap image to zoom
Workload Protection
Monitor and protect workloads in cloud environments and on-premises. Integrate with AWS, Microsoft Azure, GCP, Microsoft 365, and GitHub to monitor services, virtual machines, and platform activities. Centralized log management helps organizations adhere to regulatory requirements.
Learn More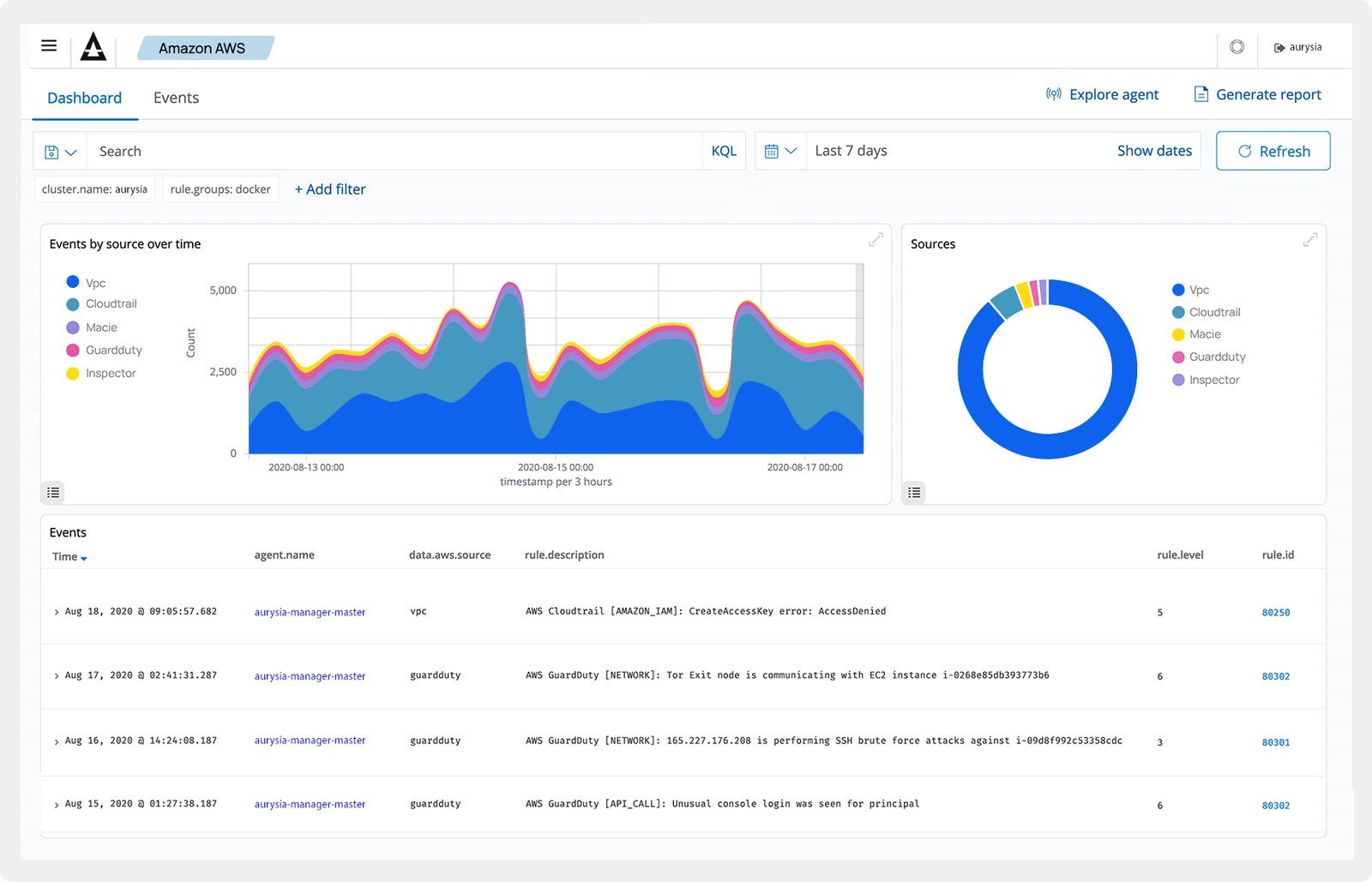
Tap image to zoom
EveryFramework.EveryAudit.Covered.
Shield generates audit-ready reports mapped to every major regulatory framework. Continuous compliance monitoring replaces point-in-time assessments — so you are always prepared, not scrambling before the auditor arrives.
PCI DSS 4.0
NIST 800-53
GDPR
HIPAA
SOC2 Type II
CIS Benchmarks
SecurityThatScalesWithYou
Flat monthly licensing based on endpoint count. No per-event fees, no surprise charges — predictable security spend that scales with your infrastructure.
$1,200
/monthFor small teams and growing organizations entering enterprise security.
- 1 month indexed retention
- 3 months archive retention
- Email support
- All 12 security modules
- Single-node deployment
- Standard compliance reports
$4,500
/monthFor mid-market enterprises requiring advanced protection and dedicated support.
- Everything in Starter
- 3 months indexed retention
- 1 year archive retention
- 24/7 priority support
- Dedicated security analyst
- Multi-node cluster deployment
Custom
Bespoke deployment for large-scale institutions with regulatory mandates.
- Everything in Professional
- Custom data retention policy
- On-premise deployment option
- SLA guarantees (99.99%)
- Dedicated threat hunting team
- White-glove onboarding
CommonQuestions
Answers for security teams and decision-makers evaluating Aurysia Shield. For anything not covered here, reach out directly.
Contact Security Team
Yourperimeterhasnoedge.Neithershouldyourdefense.
Aurysia Shield is available for enterprise deployment. Begin with a confidential consultation to scope your security requirements.
Request a Demo